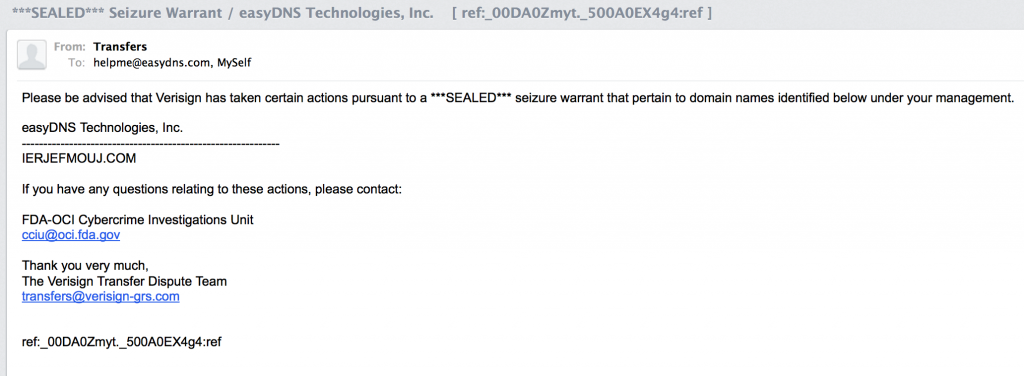
We’ve commented before on the ramifications of US agencies operating via registry operators to seize domain names. What it effectively does is put all domain names registered under .com/.net/.org/.biz under the jurisdiction of US law, for better or for worse.
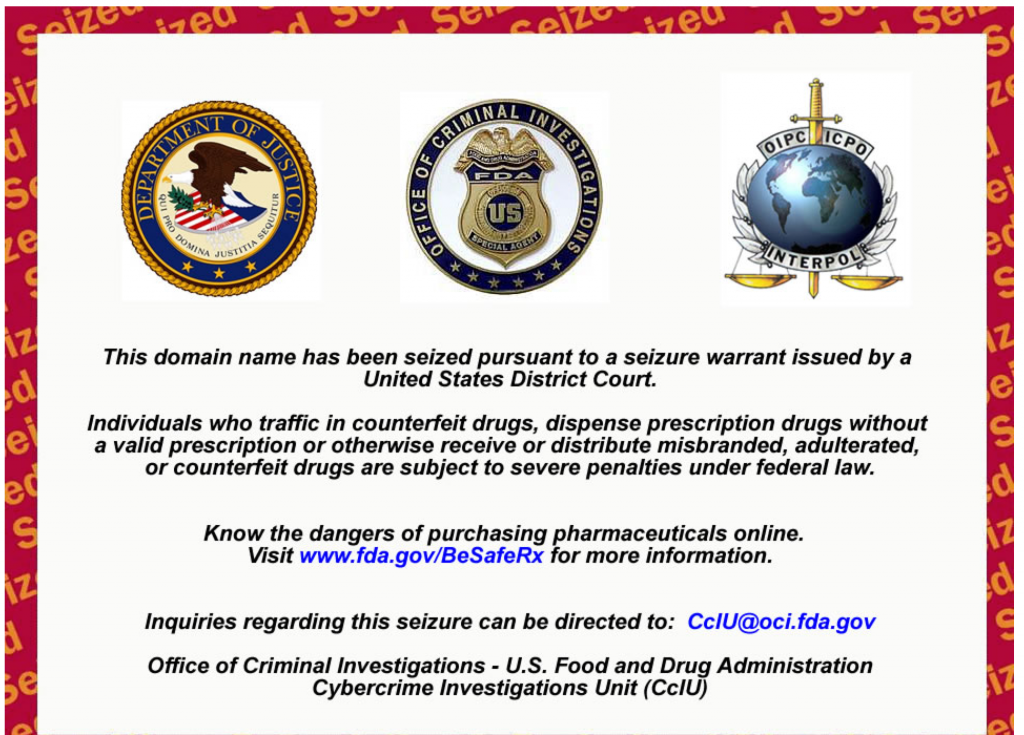
Although I have never heard of the domain name that was seized (it looks like one of those pharma sites based out of Russia), I still find the process somewhat unsettling as it makes clear that US policymakers or lawmakers can simply take any domain they want off the air first, and any questions about it have to be asked later.
As I wrote in “First they came for the file sharing domains” a few years back, it may just be some “pharma domain” today, but given the way things are heating up with whistleblowers and ever escalating government surveillance, who knows what tomorrow’s “courtesy email seizure notice” will bring?
How it’s implemented, technically
The whois record for the domain has not been altered at all and still lists the domain’s original nameservers:
NS1.QINA.RU
NS2.RXHERBALXARELTO.COM
But those are not the nameservers which are in the rootzone for the domain:
markjr$ dig +trace IERJEFMOUJ.COM
…
IERJEFMOUJ.COM. 10800 IN A 184.73.235.104
IERJEFMOUJ.COM. 10800 IN NS ec2-54-225-75-10.compute-1.amazonaws.COM.
IERJEFMOUJ.COM. 10800 IN NS ec2-54-225-74-137.compute-1.amazonaws.COM.
;; Received 163 bytes from 54.225.75.10#53(54.225.75.10) in 27 ms
Which appear to be a couple of Amazon AWS EC2 instances with a nameserver installed that just wildcards everything:
markjr$ dig +short this.com @ec2-54-225-74-137.compute-1.amazonaws.COM.
184.73.235.104
markjr$ dig +short that.com @ec2-54-225-74-137.compute-1.amazonaws.COM.
184.73.235.104
That 184.73.235.104 address, is of course, the seized domains farm…
All of which can be safely ignored provided you aren’t doing anything wrong. (You aren’t doing anything “wrong”, are you? Well …then don’t worry about it). Don’t take my word for it, Sir Tim Berners-Lee (the guy who invented the world wide web) feels the same way (sarcasm).


Leave a Reply